CASB (pronounced /kas-bee/) is the acronym for Cloud Access Security Broker. CASB is an emerging security technology that complements existing security solutions such as NextGen Firewalls (NG-FW), DLP, DPI and others. CASB addresses the issues that arise when companies start using cloud-based applications and data is no longer contained inside company boundaries.
Consider the following example: Your organisation has just decided to start using Box.com to share files and support global collaboration. Compliancy rules such as GDPR prohibit you to share personal data in your organisation outside of certain regions. Also, it is very easy - mistakenly or maliciously -to share a file with Box users outside of your organisation or with anyone on the Internet. Your NG-FW will not prevent specific data from being uploaded to Box.com as access to Box.com has been marked as a sanctioned business application. DLP functionality is limited in that it will drop or allow the transmission based on a rule set, not taking into account who is allowed access to the content from Box.com.
Access to certain data on the internal network from the outside can easily be blocked with a Firewall, but what if that data is no longer on the internal network? Issues like this limit the adaptation of cloud technologies and could force companies to continually have to support a limited amount of IT infrastructure and applications in-house. How much will vary per region, per business segment and with changing legislation.
Using a CASB solution can help overcome these concerns and enable a cloud-based IT approach without limiting its extent. Our networking, cloud and SD-WAN expertise help you choose and design the best solution for your organisation, either as a managed service or as a solution that you operate yourself.
How is CASB implemented?
A CASB solution, similar to a Firewall, must sit between the origin and the destination of the data that needs protecting. Similar to a Firewall this can be an appliance between the trusted and untrusted parts of the network, on the end point (like Windows Firewall) or in the Cloud (as a service). Each method has its drawbacks and advantages in terms of what it can achieve, how scalable it is and how complex it is to manage.
What can CASB do for my organisation?
CASB can give insights into what data is leaving your perimeter and where it is sent to. Reports include information about who (user) sent what (content type, format, keywords) where. When expanded with policies, it can also prevent data from leaving the perimeter or only allow it to be sent to specific destinations and formats (encrypted, tokenised).
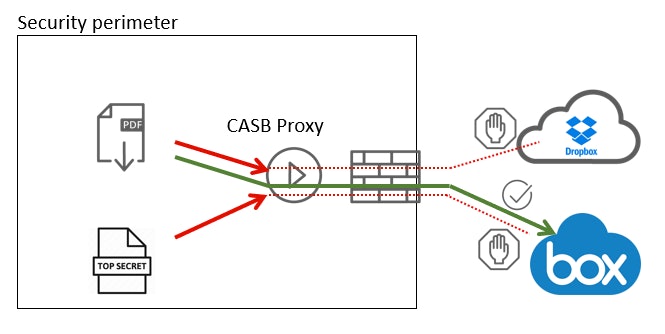
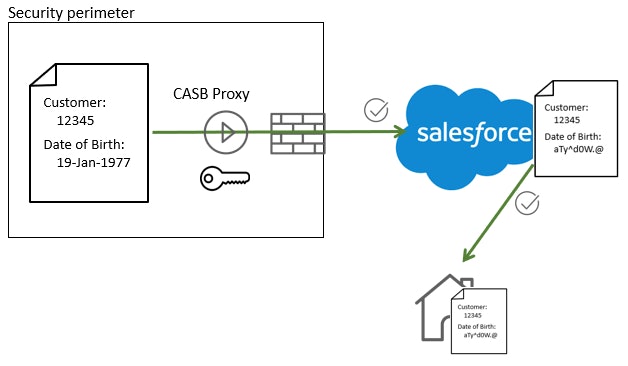
Consider the Box.com example again. The CASB device or software will sit between the client and the Box cloud. As the connection to Box is using a secure TLS connection, it will need to intercept the data before it is encrypted or act as a man-in-the-middle and intercept the TLS connection with a company trusted certificate. Data sent to Box is then monitored. When a file that is marked as confidential or containing social security numbers (or other sensitive information) is detected it will interrupt the connection and log the event. A CASB solution can also be set up to encrypt the data that leaves the perimeter. This is different from data transport encryption such as SSL. The data is encrypted on the CASB and forwarded (via TLS) to the cloud where it is stored in its encrypted format. Only when the data is retrieved via the CASB will it be decrypted again before being delivered to the user. Stolen credentials or direct access from the Internet only gives access to the encrypted data.
Because of its ability to encrypt data stored in the cloud, CASB can also help achieve GDPR compliance. Encrypted data for which the keys are not stored outside the EU does not fall under GDPR regulations, so you don’t need to worry about the compliancy of your Cloud provider and how they manage or access your data. Some CASB solutions have additional specific SaaS applications. Similar to being able to check the sharing settings for Box.com, some CASBs allow you to set rules for applications like SalesForce.com to always encrypt fields containing credit card, DoB and social security numbers. When accessing the data from outside the organisation, only non-sensitive information fields can be read.
Why should you implement a CASB solution?
As the CASB market grows more diverse and more competitive, you may be wondering whether a CASB would bring significant benefits to your organization’s cloud security. The short answer is that like any other technology, CASBs aren’t created equal. Capabilities vary, and so does effectiveness. Here are the top three benefits that the best CASBs can bring to your enterprise.
- Cloud security consolidation
- Improved compliance in the cloud
- Consistent access and identity management
Leading CASB technology partners
Get in touch with our security experts
Our team is available for a quick call or video meeting. Let's connect and discuss your security challenges, dive into vendor comparison reports, or talk about your upcoming IT-projects. We are here to help.