Introduction
XM Cyber is a global leader in hybrid cloud security. XM Cyber brings a new approach that uses the attacker’s perspective to find and remediate critical attack paths across on-premises and multi-cloud networks. The XM Cyber attack path management platform enables companies to rapidly respond to cyber risks affecting their business-sensitive systems by continuously finding new exposures, including exploitable vulnerabilities and credentials, misconfigurations, and user activities. XM Cyber constantly simulates and prioritises attack paths, putting mission-critical systems at risk, providing context-sensitive remediation options.
Do you know how you can be attacked?
Using the attacker’s perspective, you can see the attack before it happens and get a clear view of the security posture across your hybrid cloud network. Utilise full attack graphs of your exposures so you can proactively close the security gaps in your network, pinpoint and prioritise attack paths, and quickly eradicate risk in the most cost-effective manner.
Continuous Attack Visibility across Hybrid Clouds:
- Spot the hidden connections between vulnerabilities, misconfigurations, and user behaviour as it relates to an exploitable attack path, and how an attacker could move laterally.
- Reduce your attack surface by identifying where all attack paths converge on critical assets and disrupt the attack before it starts with minimum operational effort.
- Continually improve your security posture with prioritised guided remediation steps to fix what matters most.
Break the critical points in the attack chain
Illuminate and disrupt the attack paths leading to your critical assets, in the cloud or on-premises.
- Attack paths for accurate visibility of your security posture.
- On a prioritized, actionable remediation plan.
- Your overall security posture and business, continuously.

Illuminate

Act

Impact
XM Cyber Attack Path Management Platform
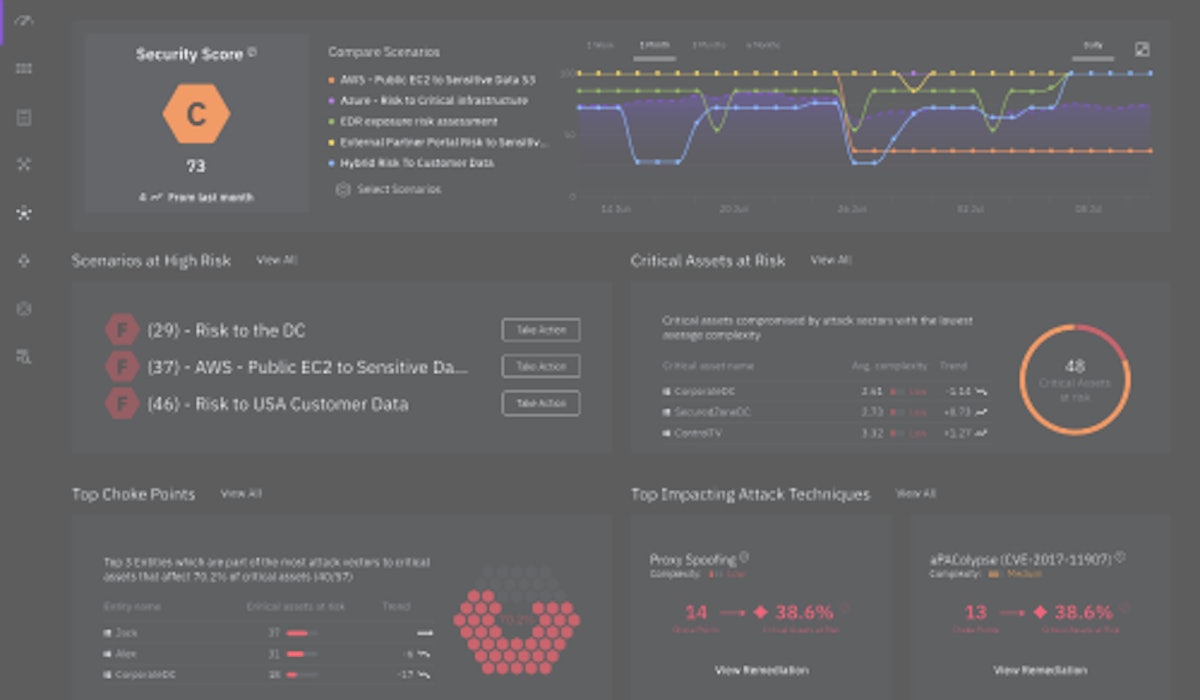
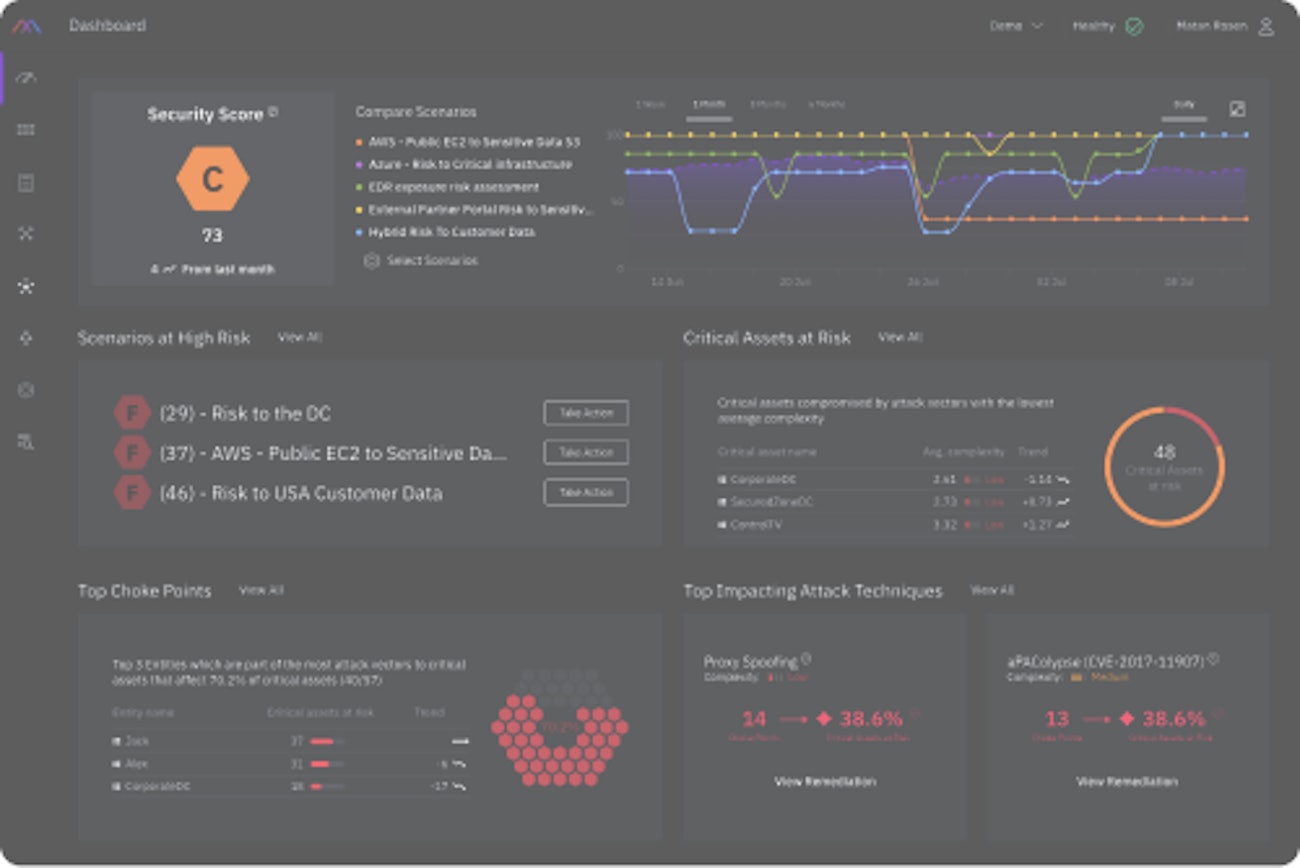
See your attack surface through the attacker’s eyes
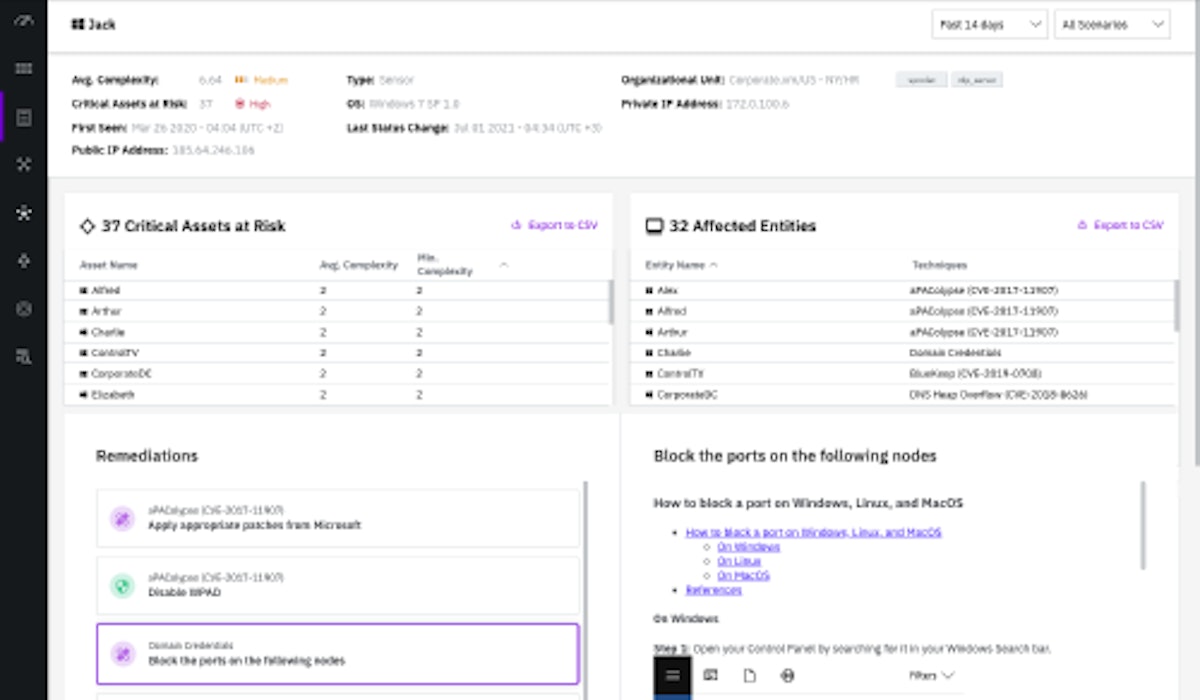
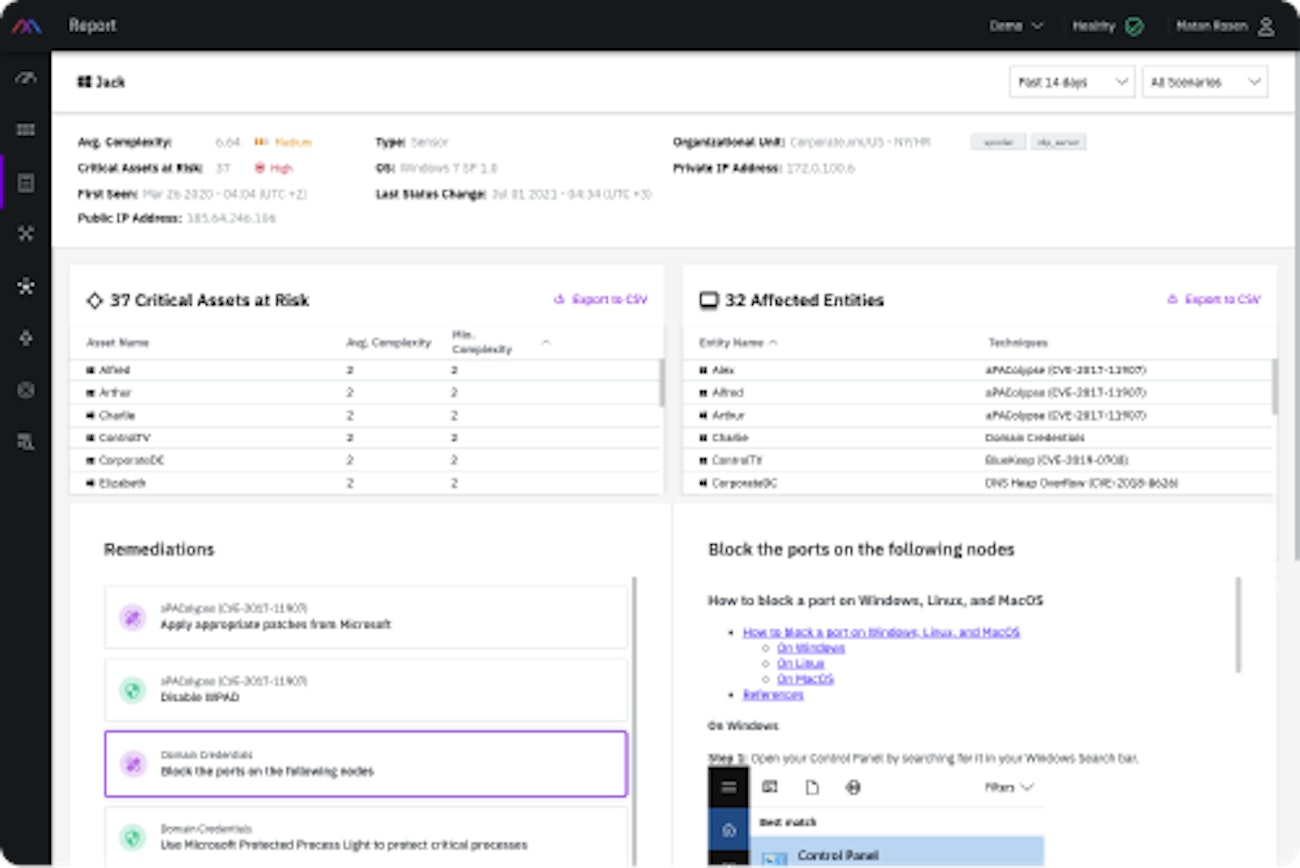
- Understand the vulnerabilities, misconfigurations, user privileges and actions that chain together to form attack paths.
- See graphical attack paths from breach point to critical assets identifying the critical choke points.
- Know the likelihood of compromise based on a constantly up-to-date security score.
Continuously fix high-risk security issues in a cost-effective manner
- Follow a step-by-step automated report that prioritizes the required actions for safe and speedy remediation.
- Accurately and effectively improve security hygiene.
- Improve your security score on an ongoing basis.
Empower your team and leverage your security infrastructure
- Make vulnerability management easy with prioritized actions and optimal use of resources.
- SaaS based platform that operates in enterprise networks (on-premise), cloud networks and hybrid environments.
- Easy integration with other security systems to leverage security investment.
Your dedicated XM Cyber experts
Nomios is an award-winning XM Cyber Affinity Global Partner with advanced specialities and the distinction of multiple certified engineers on staff. Our engineers are recognised by XM Cyber as technical experts and advocates of XM Cyber’ solutions. That means you can count on Nomios for the technical know-how and hands-on experience to accurately assess your business requirements, and design, implement and manage an XM Cyber-based solution to suit your needs.
Ready to talk?
Are you looking for pricing details, technical information, support or a custom quote? Our team of experts in Paris is ready to assist you.