Securing the Digital Frontier with Armis
In today's rapidly evolving digital world, securing connected devices and networks is more challenging than ever. Armis, as the market leader in asset intelligence, offers a groundbreaking solution to these challenges. Their platform is designed to effectively address the new threats created by connected devices.
With Armis, organisations can enjoy real-time and continuous protection, providing full context for all managed and unmanaged assets across IT, Cloud, IoT devices, medical devices (IoMT), operational technology (OT), industrial control systems (ICS), and 5G. This extensive coverage is essential in addressing today's cybersecurity challenges.
Solutions

Asset Discovery and Management
Armis Centrix™ streamlines cybersecurity asset management with visibility, real-time protection, and seamless integration.

Threat Detection and Response
Armis Centrix™ offers advanced threat detection and response capabilities for (modern) organizations, enhancing their cyber resilience.

Zero Trust Enforcement and IoT Compliance
Armis Centrix™ enhances security and compliance for OT and IoT environments through deep visibility and non-intrusive asset discovery.

Vulnerability Management and Prioritization
Armis Centrix™ transforms vulnerability management and prioritization with business impact prioritization, seamless integration, and streamlined risk management for enhanced cybersecurity.
OT/IoT Security
Armis Centrix™ offers a holistic OT/IoT security solution, blending dynamic network segmentation, compliance, asset management, and deep visibility for robust IT/OT convergence protection.
Partnership
Armis and Nomios have established a dynamic partnership, setting a new standard in the field of cybersecurity and network solutions. This collaboration brings together Armis' innovative technology and Nomios' specialised services and support, providing businesses with a comprehensive and cutting-edge approach to securing their digital environments. By partnering with Nomios, organisations can maximise the benefits of Armis' solutions, ensuring a fortified security posture, optimised operations, and exceptional performance.
Features and benefits
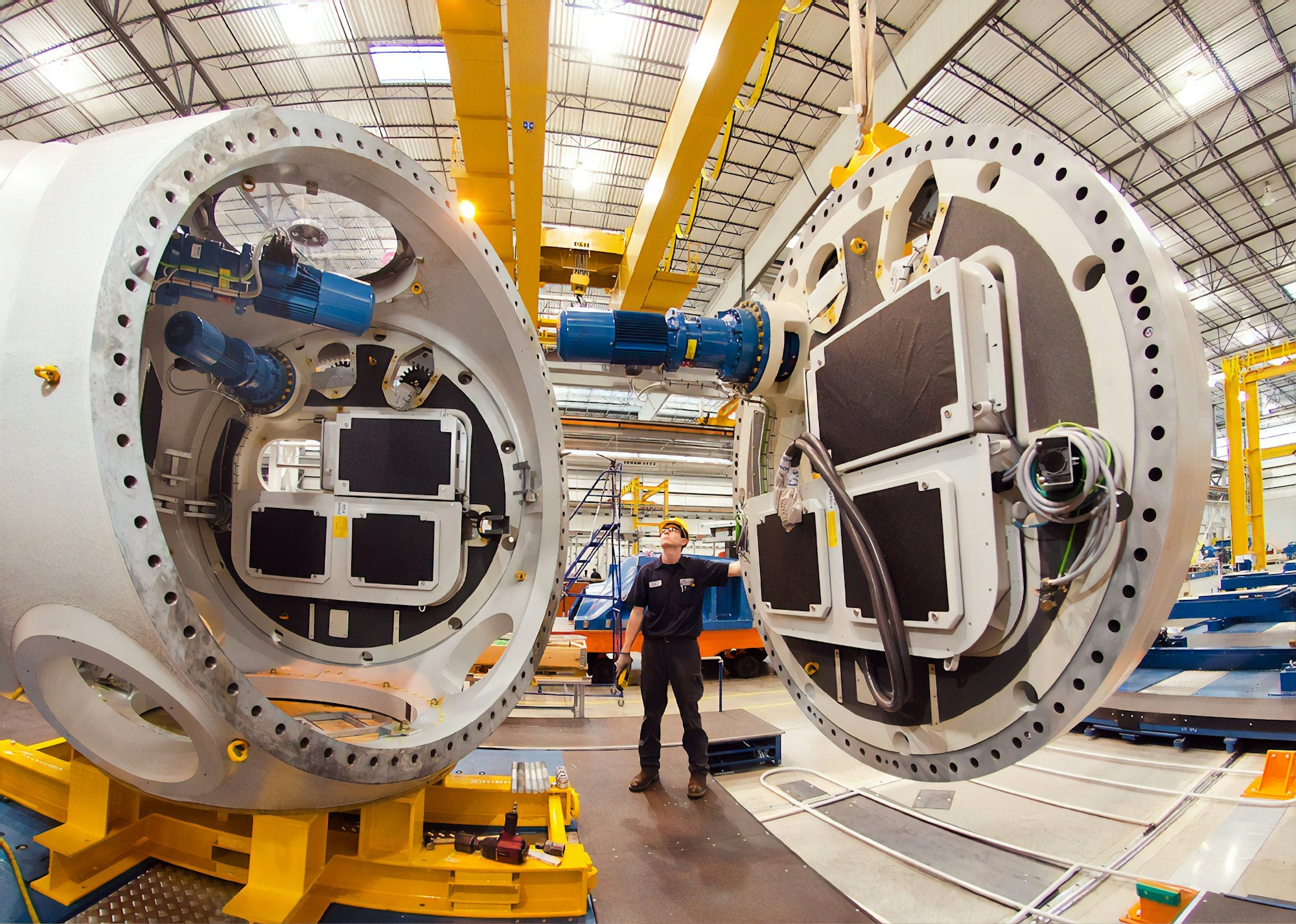
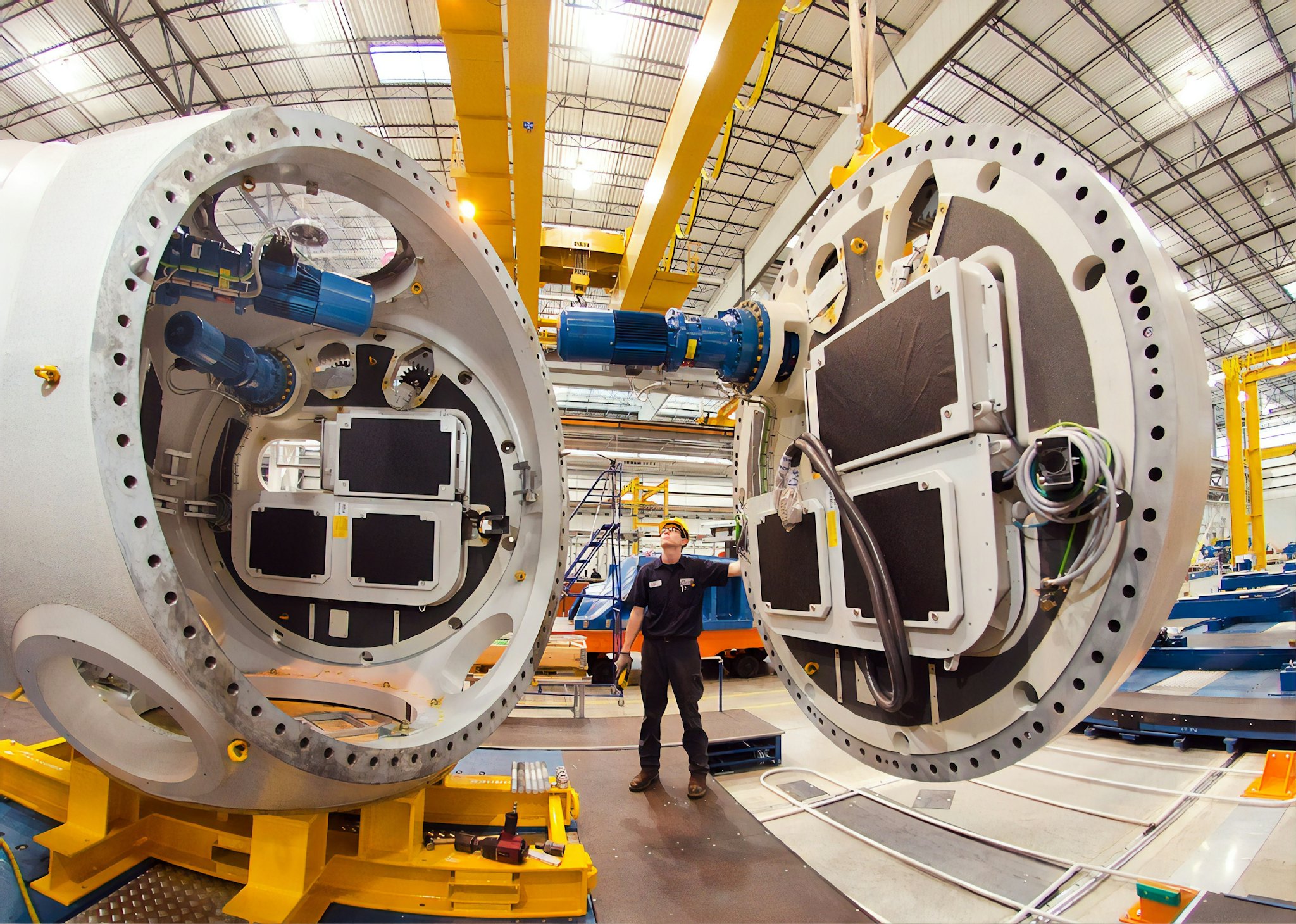
IT and OT integration
Discover, categorise and gain enriched context for every element in industrial environments, including IT devices - such as servers, laptops, IP cameras and badge readers - and operational technology (OT) such as SCADA systems, programmable logic controllers (PLCs) and distributed control systems (DCS). Prevent security issues in manufacturing with Armis Collective Asset Intelligence, the world's largest cloud-based, crowdsourced device knowledge base.

Connected heathcare
Armis identifies and secures IoMT (Internet of Medical Things), IoT (Internet of Things) and IT (Information Technology) assets critical to the delivery of connected healthcare.
The Armis Healthcare Platform is the most comprehensive Asset Intelligence platform in the industry. Gain complete visibility and maximize security of all managed and unmanaged medical devices, clinical assets and the entire healthcare device ecosystem, without disrupting patient care.
Precise discovery, complete asset visibility
Discover and locate up to 5 times more assets than your existing tools can find, including every connected clinical device, and create complete inventories in real time without manual intervention by biomedical and IT teams.
In-depth context, clinical intelligence
Rely on a unified platform for comprehensive, context-enriched views of every device, including adaptive risk assessments based on insights provided by the Armis Asset Intelligence Engine. Automatically assess devices for MDS2 properties and FDA compliance.
Continuous safety, optimised use
Manage risk and actively secure every clinical device on an ongoing basis to protect patient safety and ensure data confidentiality. The Armis Asset Intelligence Platform provides a coordinated response to near real-time cyber threats while monitoring clinical device utilisation to improve productivity and organisational resilience.
- Advanced Technology
- Armis' cutting-edge asset intelligence and cybersecurity solutions are complemented by Nomios' focus on support and services, offering a robust technological partnership.
- Expertise and Support
- Nomios' exceptional support services and deep expertise in cybersecurity and networking solutions enhance the sophisticated technology offered by Armis, delivering superior client experience.
- Flexibility and Scalability
- Our collaborative solutions are designed for adaptability and growth, aligning with your organisation's evolving requirements, with Nomios ensuring continued excellent service
- Extensive Reach
- The combined efforts of Nomios and Armis provide solutions across a wide spectrum of industries, tailoring to the unique needs of diverse clients.
- Integrated Solutions
- With Armis' advanced platform and Nomios' service-oriented approach, we ensure seamless integration and comprehensive security strategies.
- Proven Success
- The partnership of Nomios and Armis is validated by a wide range of satisfied clients across various sectors, underscoring the effectiveness and reliability of our combined solutions and services.
Proven Success: A Trusted Partner in Cybersecurity
Armis has established an impressive clientele, comprising leading organisations across various industries, including Colgate Palmolive, Allegro Microsystems, Takeda Pharmaceuticals, Mondelez, PepsiCo, the Booking Group, and many others. This diverse range of satisfied customers is a testament to the effectiveness and reliability of Armis solutions.
Armis has established itself as a private company at the forefront of cybersecurity innovation. Their platform not only offers advanced technology but also seamlessly integrates with existing infrastructures, enabling organisations to implement a holistic and effective cybersecurity strategy. Whether it's IT, IoT, IoMT, OT, or ICS, Armis provides a comprehensive solution that covers more enterprise requirements than any other vendor in the market.
Additional resources
Explore cybersecurity mastery with Armis's whitepapers. "Alignment to the NIS2 Directive" tackles operational blind spots and underscores the responsibility in outsourcing cyber services. Discover how Armis aids NIS2 compliance, from risk management to empowering SOC teams.
In "Overcoming The Cybersecurity Asset Management Challenge," unravel cybersecurity complexities, including fragmentation and control loss. Armis provides a strategic approach, addressing the crucial need for comprehensive visibility—a cornerstone in effective cybersecurity.
"Closing Hidden Security Gaps in Zero Trust Architectures" by Armis focuses on Zero Trust in the public sector. It addresses challenges with unmanaged IoT/OT assets and the importance of total network visibility. Armis's role in enhancing Zero Trust security is highlighted.
Ready to talk?
Are you looking for pricing details, technical information, support or a custom quote? Our team of experts in Zoeterwoude is ready to assist you.