Zero Trust Network Access, or ZTNA in short, ensures that you give secure access to private applications without giving the user access to the enterprise network.
ZTNA was first introduced in April 2019 by Gartner. Since then zero trust has become one of the most practised cybersecurity measures by companies, but many find it difficult to implement ZTNA fully. According to a whitepaper by ESG, 59% of IT decision-makers said that cybersecurity has become more difficult over the last two years. The main reason is remote and hybrid work. Other reasons that make it harder to manage cybersecurity are the changing threat landscape, the increase in the number of cloud applications, and the need to connect third-party users to corporate resources. Organisations have tried to implement ZTNA as a response to these cybersecurity challenges, but 54% stated that their current organisation's zero-trust initiatives have been in place for less than two years.
Challenge with implementing zero trust
What many organisations find difficult with zero trust is access controls, least-privilege access, a lack of visibility and an "allow an ignore" model that trusts but rarely verifies. Because of this, the principles of zero trust are not being followed or enforced.
That is why according to Palo Alto Networks, we need to move to Zero Trust Network Access 2.0 (ZTNA 2.0), the foundation for a new era of secure access. As ZTNA was developed as a replacement for virtual private networks (VPNs) when it became clear that most VPNs did not adequately scale and were overly permissive, the first-generation ZTNA products were still too trusting, putting customers at significant risk. ZTNA 2.0 solves these problems by removing implicit trust to help ensure organisations are properly secured.
"This is a critical time for cybersecurity. We are in an era of unprecedented cyberattacks, and the past two years have dramatically changed work — for many, work is now an activity, not a place. This means that securing employees and the applications they need is both harder and more important” Nir Zuk, Chief Technology Officer at Palo Alto Networks.
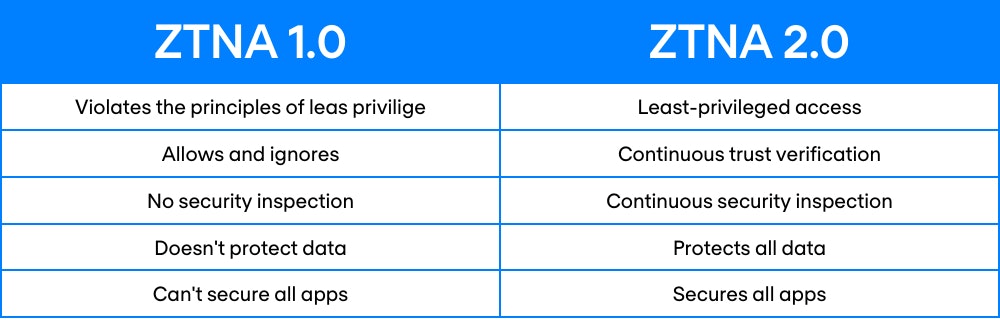
Limitation of ZTNA 1.0
For modern organisations where hybrid work and distributed applications are the new normal, ZTNA 1.0 has several limitations. As mentioned earlier, it is overly permissive in granting access to applications because it can’t control access to sub-applications or particular functions. Additionally, there is no monitoring of changes in user, application, or device behaviour, and it can’t detect or prevent malware or lateral movement across connections. ZTNA 1.0 also cannot protect all enterprise data.
Benefits of ZTNA 2.0
ZTNA 2.0 overcomes the limitation of ZTNA 1.0 and delivers on the promise of a true Zero Trust architecture. To effectively solve the shortcomings of ZTNA 1.0 approaches, ZTNA 2.0 is purpose-built to deliver:
- Least-privileged access: Identify applications based on App-IDs at Layer 7. This enables precise access control at the app and sub-app levels, independent of network constructs like IP and port numbers.
- Continuous trust verification: Once access to an app is granted, trust is continually assessed based on changes in device posture, user behaviour and app behaviour. If any suspicious behaviour is detected, access can be revoked in real-time.
- Continuous security inspection: Employ deep and ongoing inspection of all traffic, even for allowed connections to prevent all threats, including zero-day threats. This is especially important in scenarios where legitimate user credentials are stolen and used to launch attacks against applications or infrastructure.
- Protects all data: Apply consistent control of data across all apps used in the enterprise, including private apps and SaaS, with a single DLP policy.
- Secures all apps: Consistently secure all applications used across the enterprise, including modern cloud-native apps, legacy private apps and SaaS apps as well as apps that use dynamic ports and those that leverage server-initiated connections.
ZTNA 1.0 often fall short of delivering the promise of zero trust. They grant more access than is desired. Because once access is granted in ZTNA 1.0 solutions, the connection is implicitly trusted forever. This allows for a handy exploit route for advanced threats and/or malicious actions and behaviour. It is time to embrace a new approach to ZTNA, with zero trust 2.0 being one that has been designed from the ground up to meet the specific challenges of modern applications, threats, and a hybrid workforce.
ZTNA 2.0 with Palo Alto Prisma® Access
Prisma Access protects the hybrid workforce with superior security while providing a great user experience from a simple, unified security product. Purpose-built in the cloud to secure at a cloud-scale, Prisma Access protects all application traffic with the best capabilities while securing both access and data to dramatically reduce the risk of a data breach. With a common policy framework and single-pane-of-glass management, Prisma Access secures today’s hybrid workforce without compromising performance, backed by industry-leading SLAs to ensure exceptional user experiences.
Do you want to know more about this topic?
Our experts and sales teams are at your service. Leave your contact information and we will get back to you shortly.