The cybersecurity landscape is massively expanding while attack strategies keep evolving, fueling the cybercrime epidemic. Cyber threats evolved from targeting and harming computers, networks, and smartphones — to humans, cars, railways, planes, power grids and anything with an electronic pulse. Expectations are that cybercrime damages cost the world 10.5 trillion US dollars by 2025.
While costs from cybercrime are on the rise, security budgets at organisations are also growing. However, a new report from IANS Research and Artico Search indicates that the average security budget has only increased by 6% this year, which is significantly less than the increases we've seen in recent years. This suggests that the levelling off of security budgets might be part of a larger trend of cuts to IT budgets.
The challenges facing cybersecurity in the future are numerous and varied. One of the biggest challenges will be the ever-evolving nature of cyber threats. Hackers and cybercriminals are constantly developing new methods and tactics to exploit vulnerabilities, and as such, cybersecurity companies must be constantly innovating and adapting to stay ahead of these threats. The proliferation of Internet of Things (IoT) devices and the expansion of 5G networks will also present new challenges in terms of securing these devices and networks from cyberattacks.
Another challenge facing cybersecurity companies in the future will be the shortage of skilled cybersecurity professionals. As the demand for cybersecurity services continues to grow, there will be a need for more skilled professionals to fill the gap. This shortage of talent could potentially hinder the ability of organisations to effectively protect themselves from cyber threats.
Despite these challenges, the future of cybersecurity is also full of opportunities. Advances in artificial intelligence (AI) and machine learning (ML) are expected to play a significant role in the development of more effective and efficient cybersecurity solutions. Additionally, the adoption of blockchain technology has the potential to revolutionise the way in which digital transactions and data are secured.
Cybersecurity companies in 2024
In conclusion, the future of cybersecurity is expected to be characterised by increased costs, evolving threats, and a shortage of skilled professionals. However, with the advancements in technology and the development of innovative cybersecurity solutions, there is also a great deal of opportunity for companies to effectively protect themselves from cyber threats. The companies that are able to adapt to these changes and address these challenges will be the ones to watch in 2024 and beyond.
Palo Alto Networks
Palo Alto Networks, a globally recognised cybersecurity powerhouse, shields the digital domains of more than 80,000 discerning customers. With its cutting-edge Next-Generation Firewalls and cloud-based security solutions, it proudly counts over 85 of the Fortune 100 companies and three-quarters of the esteemed Global 2000 among its loyal clientele.
Consistently positioned as a leader in the Gartner Magic Quadrant for Network Firewalls for an impressive ten times in a row, Palo Alto Networks achieved yet another remarkable feat in 2023. They were not only recognised but hailed as Leaders in all three SASE-related Magic Quadrants:
- Gartner Magic Quadrant for Security Service Edge (SSE)
- Gartner Magic Quadrant for Single-Vendor SASE
- Gartner Magic Quadrant for SD-WAN
These accolades underscore Palo Alto's undisputed leadership in the dynamic SASE market. Their SASE solutions are meticulously designed to safeguard organisations, offering protection against a broad spectrum of cyber threats, including malware, ransomware, and phishing attacks.
In June 2023, Palo Alto Networks unveiled Prisma Cloud 3.0, a robust cloud security platform that provides comprehensive protection for cloud-native applications and workloads. A couple of months later, in October 2023, they upgraded the Prisma Cloud platform with "code to cloud" intelligence. This new feature offers a single source of truth for application risk. It benefits developers, operations, and security teams. The latest version, called the Darwin release, adds several capabilities. These help organisations address security risks early in the production cycle. They also integrate changes throughout the cloud workflow.
Just three months later, in September, they introduced the Cortex XDR Platform, a security powerhouse that seamlessly integrates data from across the security landscape, empowering organisations with extended detection and response (XDR) capabilities.
October 2023 marked a significant milestone as Palo Alto inaugurated its new EMEA and LATAM head office in the iconic "Valley" of Amsterdam, The Netherlands. This state-of-the-art workplace, designed to accommodate 350 employees, embodies sustainability and collaboration. It underscores the company's commitment to expanding its operations to better support its growing customer base in EMEA and Latin America.
Even for a company of Palo Alto's caliber, there's always room for improvement. It's our belief that expanding their cloud security offerings is essential to meet the surging demand for cloud security solutions. Additionally, developing more integrated security solutions, rather than marketing and selling them separately, would be a significant stride forward.
Acquisitions by Palo Alto Networks
In 2023, Palo Alto Networks added two more feathers to its cap through acquisitions:
- Orca Security: This acquisition, completed in June 2023, brought aboard a company specialising in cloud security for cloud-native workloads.
- Dig Security: In July 2023, Palo Alto Networks welcomed Dig Security into its fold, further solidifying its presence in the realm of cloud security for cloud-native infrastructure.
CrowdStrike
Since its founding in 2011, CrowdStrike has been revolutionising cybersecurity. The CrowdStrike Falcon endpoint protection platform, designed from the ground up, stands as an impenetrable fortress against modern cyberattacks. With a single lightweight agent, it offers prevention, detection, threat hunting, response, remediation, vulnerability assessment, and IT hygiene—all in one package.
Central to CrowdStrike's arsenal is the Falcon Prevents framework, a game-changer that bestows five-second visibility upon all endpoints, both past and present. This visionary approach not only enhances security but also streamlines costs and simplifies complexity. CrowdStrike's cybersecurity services span the spectrum, encompassing threat intelligence, next-gen antivirus, incident response, ransomware interception, and endpoint detection and response.
In a pursuit of innovation, they launched Falcon XDR 7.0 in August 2023. It includes a number of new features and enhancements, including new threat hunting capabilitys that uses ML and AI, improved integration with third-party security tools and enhanced performance and stability.
Within the pages of the CrowdStrike 2023 Global Threat Report, a comprehensive account of the contemporary cyber threat landscape emerges. The report delves deep into the real-world scenarios and observed trends in the ever-evolving tactics, techniques, and procedures employed by adversaries. It offers pragmatic recommendations designed to fortify your organisation for the challenges that lie ahead.
Last year CrowdStrike saw that the threat landscape became more crowded as new adversaries emerged. Ransomware remains as the most prominent cyber menace, with adversaries targeting cloud environments and employing ever-sophisticated evasion techniques. To thwart these threats, a multi-layered security approach, coupled with the diligence of keeping systems and software up to date, and the education of employees in cybersecurity best practices, have become indispensable. Noteworthy adversary developments include:
- A 20% surge in ransomware attacks.
- A staggering 95% uptick in cloud exploitation.
- A 71% spike in malware-free attacks.
- A 112% increase in access broker ads on the dark web.
- An average of 84 minutes to compromise and 282 days to detect a breach.
When examining avenues for further enhancement, CrowdStrike is poised to expand its endpoint security offerings by incorporating advanced features. The pursuit of robust endpoint security features is critical to safeguarding customers against emerging threats. Additionally, consolidating security products into more integrated solutions is on the horizon—a strategic move that will seamlessly unite the customer experience and elevate security measures to new heights.
Acquisitions by CrowdStrike
In the year of 2023, CrowdStrike bolstered its portfolio through a strategic acquisition:
- Bionic: This visionary acquisition, finalised in September 2023, ushered in a new era of application security posture management (ASPM) solutions under the CrowdStrike umbrella.
Cisco
Cisco stands tall as a frontrunner in the realm of cybersecurity, offering an extensive array of security solutions meticulously crafted to shield organisations from the ever-evolving threat landscape. Within their arsenal lie an impressive suite of security products and services, including firewalls, intrusion prevention systems, secure web gateways, cloud security, and the cutting-edge realm of security automation.
As we delve into the dynamic world of cybersecurity, the emergence of SASE takes centre stage. Cisco, ever the trailblazer, has positioned itself as a Visionary in the Gartner Magic Quadrant framework for Single-Vendor SASE. But they're not merely content with their current status; Cisco has embarked on a journey of substantial investment in SASE in 2023, and the road ahead in 2024 promises even more innovation.
Among the captivating enhancements introduced to Cisco's SASE solutions, integration with SecureX, their XDR (Extended Detection and Response) platform, takes the spotlight. It now boasts robust zero-trust security capabilities, elevating security posture management to new heights.
Cisco's footprint extends beyond SASE, as evidenced by their presence in multiple Gartner Magic Quadrants:
- Gartner Magic Quadrant for Network Firewalls (Leader, 10th consecutive year)
- Gartner Magic Quadrant for Security Information and Event Management (SIEM) (Leader)
- Gartner Magic Quadrant for Endpoint Protection Platforms (Challenger)
- Gartner Magic Quadrant for Managed Detection and Response (MDR) Services (Challenger)
Yet, as we juxtapose Cisco with its competitors, we discern areas ripe for refinement. Their endpoint security and MDR solutions, while formidable, are not as firmly established as some rivals. To retain their eminent leadership in the broader security landscape, Cisco must persist in their investments in these domains. A recurrent refrain from their valued customers is the complexity associated with their security portfolio—a complexity they wish to simplify. Streamlining their product offerings to facilitate customer choices and deployments emerges as a pivotal improvement on their horizon.
Acquisitions by Cisco
In the transformative year of 2023, Cisco fortified its arsenal through the strategic acquisition of two visionary security companies:
- Opsani: Pioneers in cloud-native security observability solutions, Opsani was brought under Cisco's wing in January 2023.
- Splunk: A stalwart in the realm of data observability and security software, Splunk found a new home within Cisco in September 2023.
The acquisition of Splunk, in particular, bears profound implications. It elevates Cisco into the upper echelons of data observability and security solution providers. With Splunk's software gracing the arsenals of some of the world's largest and most sophisticated organisations, this acquisition presents Cisco with an unprecedented opportunity to cater to a broader customer base and harness a new spectrum of capabilities.
Fortinet
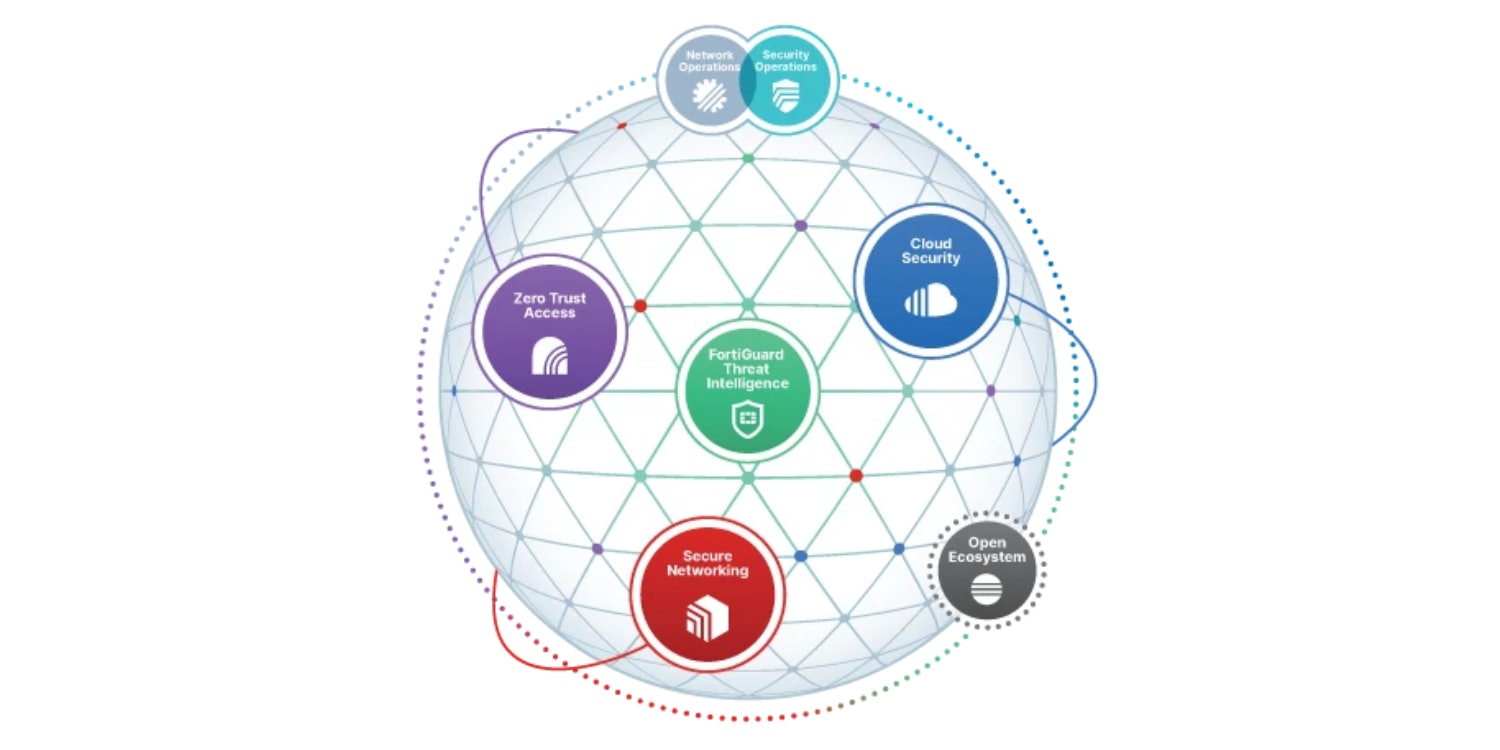
Fortinet stands as a global cybersecurity juggernaut, renowned for its expansive, integrated, and automated defence mechanisms against the most formidable cyber threats. Their cybersecurity solutions serve as a stalwart shield for organisations of all sizes, extending their protective embrace to Fortune 500 enterprises, service providers, and government agencies alike.
At the core of Fortinet's security prowess lies the Fortinet Security Fabric—a cohesive, unified platform that blankets the entire digital infrastructure with end-to-end protection. This remarkable fabric seamlessly weaves networking, security, and analytics into a comprehensive shield, offering unparalleled defence against cyber threats.
Within the dynamic realm of Single-Vendor SASE providers, Fortinet emerges as a Challenger, bearing the FortiSASE standard. While their SASE platform continues to evolve, it promises to secure your hybrid workforce, boasting a modern zero-trust architecture that begets network and security visibility spanning your entire organisation.
Beyond the realm of SASE, Fortinet's Zero Trust security portfolio has blossomed with new solutions catering to micro-segmentation, identity and access management (IAM), and SIEM. Their strides in Zero Trust have not gone unnoticed, earning them the distinguished title of Leader in the Forrester Wave for Zero Trust Edge Solutions of Q3 2023.
As Fortinet charts its course into 2024, opportunities for enhancement beckon. Strengthening the integration between its products and services, augmenting cloud security offerings, bolstering SOAR (Security Orchestration, Automation, and Response) capabilities, and fortifying security for emerging technologies will ensure that Fortinet retains its mantle as a leader in the cybersecurity arena.
Acquisitions by Fortinet
In the transformative year of 2023, Fortinet expanded its arsenal through a strategic acquisition in the realm of NDR (Network Detection and Response):
- Gigamon ThreatInsight NDR business: This solution harnesses the power of machine learning and artificial intelligence to detect and counter advanced cyber threats.
Fortinet plans to rebrand this technology as FortiNDR Cloud, offering it as a cloud-based complement to their existing on-premises FortiNDR product (formerly known as FortiAI).
Furthermore, Fortinet had earlier acquired a commanding 75% stake in Alaxala Networks Corporation in 2021—a provider of cloud-native security solutions for Kubernetes environments. Fortinet has seamlessly integrated Alaxala's technological prowess into their FortiWeb Web Application Firewall (WAF) product, further fortifying their cybersecurity arsenal.
Talk with our cybersecurity experts today
Our European cybersecurity experts are available now for a call or video meeting. Let's talk about your network challenges, discuss solution suitability, or talk about vendor solutions or upcoming network projects. We are here to help.

Juniper Networks
Within the dynamic realm of cybersecurity, Juniper Networks takes the helm, engineering security products that stand as unyielding sentinels against an array of threats, from the relentless surge of cyberattacks to the ever-looming spectre of malware and data breaches. Among the notable milestones in cybersecurity was the unveiling of Juniper Secure Edge in Q1 2023—a watershed moment in their journey.
Juniper Secure Edge, the crowning jewel of their endeavours, ushers in the era of SSE. This groundbreaking offering safeguards web, SaaS, and on-premises applications, ensuring that users enjoy a seamless and secure experience, regardless of their location. When paired with Juniper's AI-driven SD-WAN, it births a best-in-class SASE solution.
In 2023, Juniper Networks continued to invest in Security Director Cloud. It's their portal to SASE, bridging current security deployments with future SASE rollout. Juniper Security Director Cloud helps organisations migrate securely to SASE architecture. Using Juniper Security Director Cloud, organisations can create unified policies once and deploy the policies wherever their users are using the applications. Unified policy management ensures seamless security across all users, applications, or devices wherever they are.
Among Juniper's celebrated products, Mist stands as a beacon. This cloud-managed network solution, powered by AI, harmoniously integrates with the Connected Security framework. The synergy of AI enhances visibility into user and device behaviour while automating the detection and mitigation of threats, catapulting cybersecurity to new frontiers.
Furthermore, Juniper is proud to announce a paradigm shift in network access control (NAC) with the expansion of its Juniper Mist AI-driven enterprise portfolio, Juniper Mist Access Assurance. This cloud-based NAC service enables enterprises to easily enforce secure network authentication and authorisation. Alongside, Juniper Security Director Cloud bridges current security deployments with future SASE rollout, helping organisations migrate securely to SASE architecture.
Juniper Networks received “AAA” ratings in CyberRatings.org’s Enterprise Network Firewall evaluation, achieving the highest security effectiveness score of 99.94%. These accolades are a testament to Juniper's commitment to providing unrivalled security solutions. The new generation of SRX firewalls, which will be available in January 2024, represents another milestone in this regard. With built-in zero-trust and throughput rates up to 1.4Tbps, the new Juniper firewalls represent AI-driven protection that simultaneously increases operational energy efficiency.
Juniper Networks offers a formidable array of security products, yet the puzzle remains incomplete. The challenge lies in the integration of these products. In 2024, Juniper has an opportunity to seamlessly weave these offerings together, simplifying the management of security postures for organisations and empowering them to navigate the complex cybersecurity landscape with greater ease and efficacy.
Do you want to know more about cybersecurity? Then download the whitepaper 'Understanding the basics of cybersecurity'. It covers the fundamentals of information security, what it does, and why it's so important.
Vectra AI
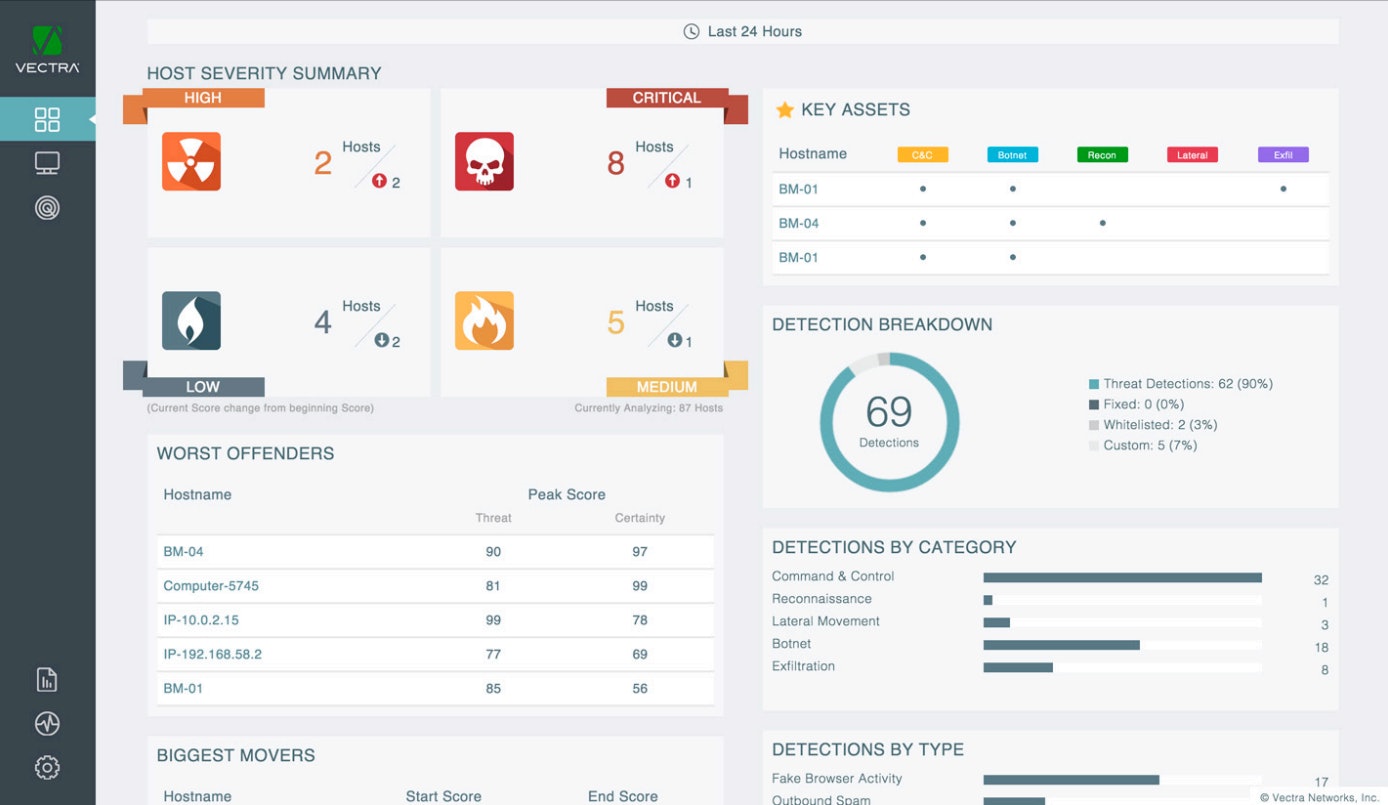
In the realm of cybersecurity, Vectra AI emerges as a formidable force, offering AI-driven solutions that redefine threat detection and response. Their mission is clear: to empower organisations with the ability to detect and combat cyberattacks in real-time, regardless of their complexity or evasiveness.
The year 2023 marked a triumphant chapter in Vectra's journey through the cybersecurity landscape. They earned the distinguished title of Leader not once, but twice. Firstly, in the Gartner Magic Quadrant for Network Detection & Response (NDR)—a commendable achievement for the third consecutive year. Secondly, in the Forrester Wave for Network Security Monitoring and Response (NSMR), solidifying their leadership for the second year running.
Within the pages of the 2023 State of Threat Detection report, Vectra AI unveiled key insights gleaned from a survey of 2,000 security analysts spanning the globe. The findings unveiled a stark reality—the relentless surge in cyberattacks has left security analysts grappling with the formidable challenge of maintaining vigilance:
- A staggering 71% of analysts harbour concerns that their organisations may have fallen victim to cyberattacks that remain concealed.
- A significant chunk of their precious time is devoured by manual tasks, from alert triage to incident investigation.
- Confidence in the efficacy of existing security tools wanes, with a mere 31% of analysts expressing strong confidence in their tools' ability to thwart cyberattacks.
As Vectra AI sets its sights on the horizon of 2024, avenues for growth beckon. Expanding support for cloud-native environments stands as a pivotal opportunity. The burgeoning market for cloud-native solutions offers fertile ground for further support and development. While Vectra AI has already harnessed the power of AI and machine learning in their security products, continued investment in these technologies will further fortify the security prowess of their solutions, ensuring organisations remain one step ahead in the ever-evolving cybersecurity landscape.
F5
F5 stands as a stalwart guardian, offering a comprehensive suite of enterprise security solutions designed to safeguard organisations across the vast expanse of the digital landscape. Their solutions are versatile, adapting seamlessly to any environment, whether your applications reside on-premises or span the spectrum of private, public, or multi-cloud deployments.
Within the arsenal of performance and security services that F5 provides, one finds a panoply of defences. From load balancing to DNS services, web application firewalls (WAF), identity and access federation, to the critical bastion of DDoS mitigation—F5 leaves no stone unturned.
In the digital age, applications power businesses both great and small. Yet, even as they fuel progress, they stand as a focal point for relentless attacks. F5 recognises this dichotomy and rises to the challenge with a suite of robust security solutions.
The year 2023 witnessed a pivotal moment with the release of a new iteration of F5's BIG-IP platform. This update ushered in a host of cutting-edge security features, including fortified bot protection and the orchestration and remediation of application security. Furthermore, it extended its protective embrace to a broader range of cloud platforms, including Google Cloud Anthos, Microsoft Azure, and AWS Outposts.
With F5's Advanced WAF, organisations gain a bulwark against the latest threats. It leverages behavioural analysis, proactive bot defence, and application-layer encryption to safeguard sensitive data, including login credentials. Their unwavering commitment to excellence shines through as F5 clinches leadership positions for the eighth consecutive year in both the Gartner Magic Quadrant for Web Application Firewalls and the Forrester Wave: Web Application Firewalls.
While F5 holds a prominent position in the cybersecurity arena, the path to 2024 beckons with opportunities for enhancement. Like many industry peers, F5 can further improve the integration of their security solutions—a move that would simplify the implementation and maintenance of comprehensive cybersecurity postures for organisations. Additionally, a continued investment in advanced threat detection capabilities, such as machine learning and AI algorithms, will enable them to identify and thwart emerging threats with greater effectiveness and real-time precision.
Acquisitions by F5
In 2023 F5 expanded its arsenal through a strategic acquisition in the realm of cloud computing:
- Lilac Cloud: a provider of innovative application delivery services. Lilac Cloud's technology is used in F5's Distributed Cloud Services platform.
The acquisition of Lilac Cloud is part of F5's strategy to expand its portfolio of application security and delivery solutions. Lilac Cloud's technology will help F5 provide its customers with even more comprehensive and effective protection for their applications and data.
New and noteworthy cybersecurity companies for 2024
As we step into the new year of 2024, we'd like to introduce three remarkable organisations worth keeping an eye on: Venafi, Wallix, and TEHTRIS. These companies are poised to make significant contributions to the cybersecurity landscape.
Venafi
Based in the United States, Venafi is a leader in Machine Identity Management (MIM) solutions. Their mission is to ensure secure communication between machines through digital identities. Their technology plays a vital role in sectors such as banking, insurance, and telecommunications, helping safeguard operations and client data. Venafi also assists organisations in complying with the stringent Payment Card Industry Data Security Standard (PCI DSS) regulations, enhancing their cybersecurity framework.
WALLIX
WALLIX, headquartered in France, specialises in Privileged Access Management (PAM) solutions. Privileged account access regulation is a crucial aspect of cybersecurity, particularly for sectors like government, finance, and healthcare. Wallix's technology helps protect privileged accounts from unauthorised access, reducing the risk of data breaches. It also aids organisations in complying with the General Data Protection Regulation (GDPR).
TEHTRIS
TEHTRIS, proudly rooted in Europe and originating from France, distinguishes itself in the cybersecurity arena with its cutting-edge Extended Detection and Response (XDR) solutions. These invaluable offerings cater to organisations across various sectors, providing a comprehensive view of security data. TEHTRIS excels in streamlining security operations, automating processes, and responding swiftly and effectively to cyber threats, thereby enhancing overall security. Their cyber defence solutions proudly present a comprehensive "made in Europe" answer to combat cybercrime and sabotage, all within a single, unified interface.
Overall, Wallix, Venafi, and TEHTRIS are three new and noteworthy cybersecurity companies that are developing innovative solutions to help organisations protect themselves from the latest cyber threats. Together with the other companies mentioned above, they are all companies to watch in 2024 and beyond.
Nomios’ cybersecurity vendors
These vendors form the foundation of our cybersecurity architecture, designed to support our customers in transitioning to a Zero Trust Access, Secure Services Edge (SSE), and Secure Access Service Edge (SASE) architecture. Combining the innovative capabilities of these cybersecurity leaders with Nomios' local expertise is a key factor in achieving a successful security architecture transition. This approach aims to maximise security, minimise costs, and provide the best user experience with IT services, ultimately boosting productivity.
However, as each organisation is unique, the ideal solutions may vary. At Nomios, we are here to assist you in finding the cybersecurity solution that aligns with your specific needs.
Do you want to know more about this topic?
Our experts and sales teams are at your service. Leave your contact information and we will get back to you shortly.